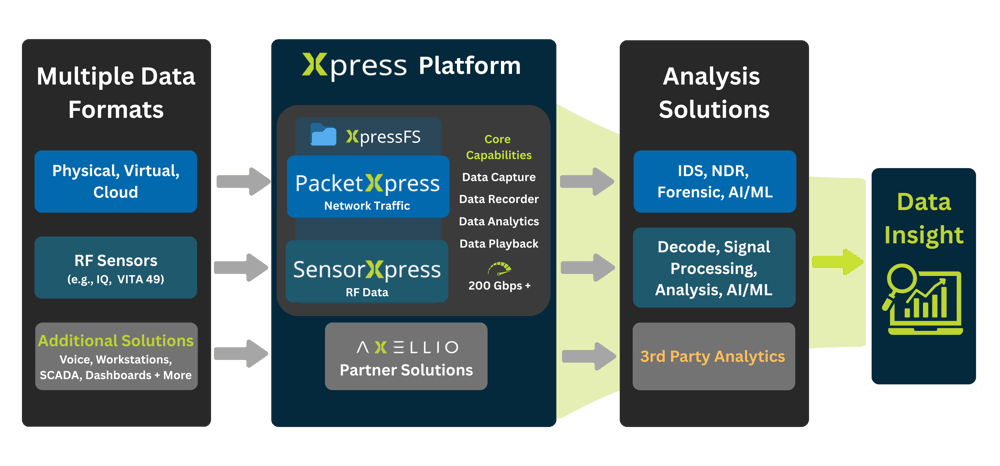
Your Fast Track to Real-Time Data Insight
Axellio’s Xpress Platform® is a software-based data intelligence solution that can handle any data speed - including speeds of 200 Gbps and higher. Its unique architecture allows simultaneous reading, writing, and storing of any time series data.
Two Solutions to Capture, Manage, and Understand YOUR Data
.png)

PacketXpress — Network Intelligence for Cybersecurity & Network Operations
Simultaneously capture, store, and distribute full PCAP network traffic at over 200 Gbps in just 1RU
Supercharge Your Network
Experience unmatched speed, scalability, and visibility with PacketXpress, a powerful platform to capture, store, analyze, and share your network traffic.
✔ Boost your network security monitoring and forensic analysis
✔ Analyze full packet data – not just metadata
✔ Cut down on licensing costs and operational complexity
✔ Integrate seamlessly with your existing tools and workflow
SensorXpress — Innovative RF Data Capture, Storage & Distribution
Reliably analyze Radio Frequency data, SWaP optimized to capture petabytes of data
Never Miss a Signal of Interest
Unlock real-time spectrum awareness with SensorXpress, a high-performance platform to monitor, record, analyze, and share RF data across any mission.
✔ Frequency, protocol, and hardware agnostic
✔ Software-based RF data recording and distribution
✔ Ingest, store, and distribute 200 Gbps in just 1RU
✔ Record more spectrum over longer durations
✔ Low SWaP for Edge and tactical operations
✔ Vendor-agnostic for easy integration with existing systems


-1.png?width=250&height=100&name=Untitled%20design%20(47)-1.png)










-1.png?width=250&height=100&name=Untitled%20design%20(48)-1.png)


-1.png?width=250&height=100&name=Untitled%20design%20(47)-1.png)










-1.png?width=250&height=100&name=Untitled%20design%20(48)-1.png)
PRIME CONTRACT VEHICLES
Axellio products are available on the following IDIQ vehicles:
- NASA SEWP V
- Army ITES-SW2
- MDA SHIELD
Please contact us for additional information or other contracts.
CERTIFICATIONS
- ISO 9001:2015 Certified
- DoD Authority to Operate (ATO) on NIPR & SIPR
.png?width=120&height=60&name=PERRY%20JOHNSON%20(3).png)
TRADEWINDS MARKETPLACE
The Tradewinds Solutions Marketplace is the premier offering of Tradewinds, the Department of Defense’s (DoD’s) suite of tools and services designed to accelerate the procurement and adoption of Artificial Intelligence (AI)/Machine Learning (ML),data, and analytics capabilities.


.png?width=591&height=355&name=PX%20Spider%20Graphic%20V1%20(14).png)




